Interesting question raised by a former newspaper colleague and a Poynter institute column: “Should journalists play a role in identifying rioters?”
That’s the headline and based on it alone, the answer is, of course. Media goes after the facts and a big chunk of the facts from last week’s Washington riot answers the question: Who the hell were these people?
The more-specific and thornier question is: “Should the media turn over unpublished documentation, especially photographs, to law enforcement upon request?”

Every new generation of journalists grapples with this one, even if the answer is almost always the same.
During my entire career, the answer was invariably a solid NO.
Once journalists start “assisting” law enforcement, any claims of being an objective observer are gone. And with it goes the ability to claim the role of neutral observer during live events. That puts the lives of journalists in jeopardy and it inhibits the ability to cultivate opposition sources.
Easy for me to say. Nobody has ever asked for my notes on rock concerts or consumer technology stories or transportation reporting …
In the real world, maybe individual journalists would have to weigh the gravity of the crime against the value of unpublished photos or interviews and ask: If they are that valuable, why aren’t they already published?
If I had a photograph or information that could save hundreds of lives, why wouldn’t I offer it up?
What is fascinating in today’s world is that the unpublished images of old school media may be less and less critical to any investigation.
First, newspaper websites are able to publish an endless number of supplementary images. If you’ve got ‘em, upload ‘em. Why leave good stuff in the (now metaphorical) darkroom?
Second, social media is doing the job for law enforcement. Last Wednesday’s march was probably the biggest social media event in history. Rioters and miscreants were uploading selfies, spinning streaming media coverage, posing for photos, identifying each other, and generally self-identifying themselves and their locations for the world to see. And most were doing so without covering their faces with anti-COVID masks.

It is easy to think they were extraordinarily dumb on so many levels but also incredibly naive about the consequences of their blatant law-breaking. Just because thousands do it, doesn’t make it right.
But it is sure making it easier for law enforcement and online social-justice warriors to do their job. Even though it seems a lot of these white guys ran home and shaved off their beards right away. Great disguise, guys!
Add to this the enormous CCTV camera content, cell-phone tower data, and scores of amateur Internet sleuths who are hunting down rioters — and they are discovering that they have nowhere to run, nowhere to hide.
My favorite was the Michigan dad who proudly reposted a picture of his son posing with the statue of Gerald Ford in the Hall of Statuary. His next post was “Why is the FBI trying to contact me?”
Followed by the woman who recognized her ex-husband heavily mocked up in combat gear. She turned him in.
Third, techies and online “bounty hunters” are helping law enforcement identify the rioters in surprising numbers and in some surprising places: According to the Washington Post, in the days leading up to the riot, local dating sites like Bumble and Tinder saw a serious uptick in MAGA hatted men with #StopTheSteal hashtags. Some added poses on the Capitol steps.
It is not a big leap from connecting ersatz dating photos to selfies uploaded inside the Capitol.
More productive though, are the legion of researchers who have been tracking right-wing extremists online and tracing photos and selfies from the Capitol.
These social media researchers have been “doxing” the rioters — publicizing information about them, sometimes leading to arrest and sometimes leading to companies firing the seditionists.
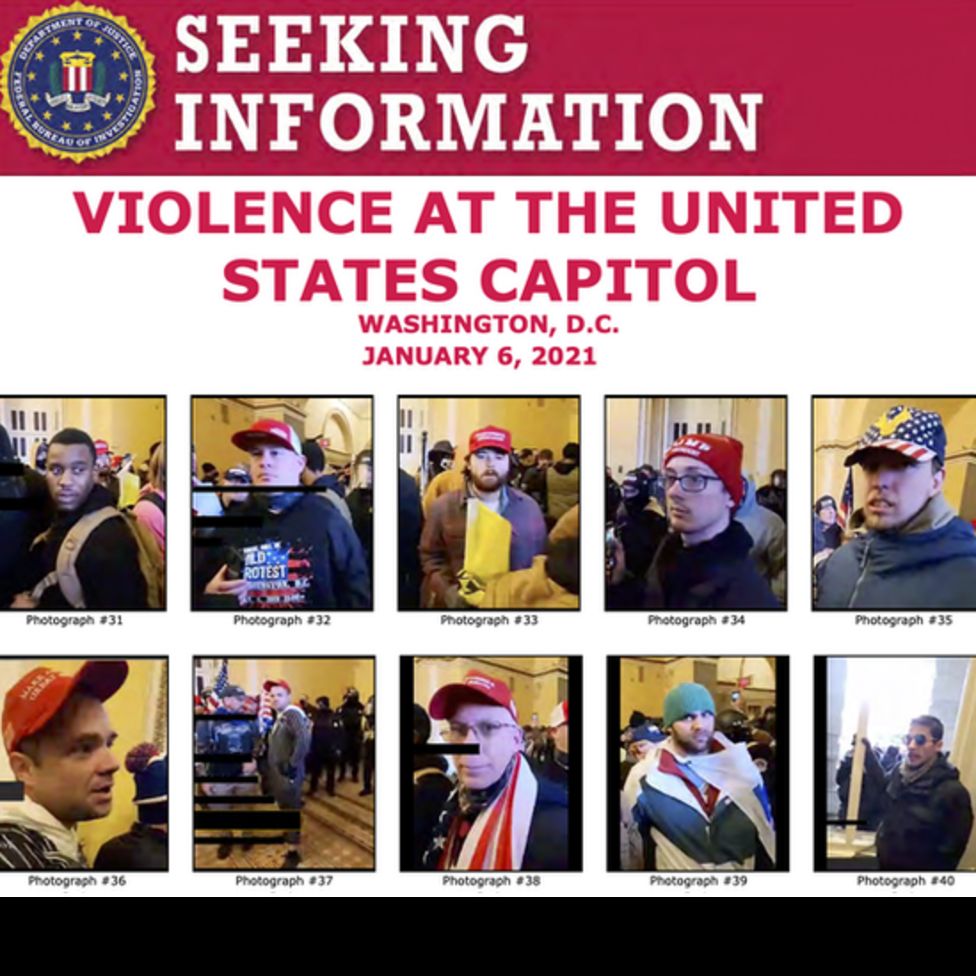
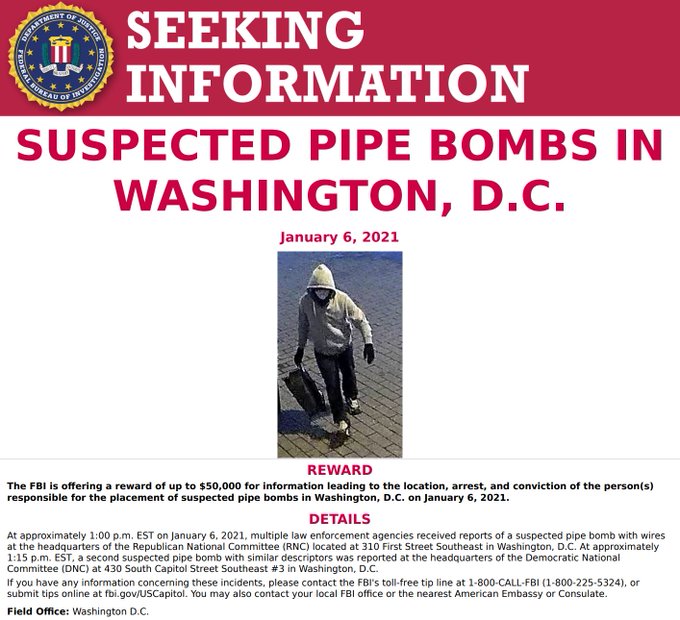
The FBI harvested scores of images of participants and has been sending them out on social media, seeking the public’s help in identifying them. Plenty of people with no journalism connections have been happy to help. Law enforcement and dark-cover sleuths are also using sophisticated facial recognition software like Clearview AI to track down rioters.
It is a weird world in which some live-streaming rioters on DLive for example were able to make more than $2,000 from their fan base by publicizing their crime in progress. Meanwhile, the FBI is offering $1,000 for information leading up to the arrest of some of these people.
Law enforcement doesn’t even need pictures. If your cell phone was on, you have been outed.

Combine cell data with the extraordinary number of uploaded photos and videos and the prevalence of sophisticated facial recognition software and there is — as I said — nowhere to run, nowhere to hide. (I love saying that.)
And they can’t take stuff down fast enough to escape detection. Hackers claim that they broke into the right-wing nest called Parler and downloaded 70 terabytes of communications, photos — everything — before Amazon pulled the web-hosting rug out from under it. The data has been uploaded and crowd-sourcing techies are tearing it apart for background on who planned, promoted, and participated in the riot.
Crowd-sourcing the identity of rioters is beginning to look like shooting ducks in a barrel.
“… private researchers and ordinary individuals scrutinized online video and photos, they identified some of those who took part and assisted law enforcement, according to NPR.
John Scott-Railton from Citizen Lab at the University of Toronto noticed that a number of people in paramilitary uniforms were acting more purposefully than the average rioter. They clearly seemed on a mission inside the Capitol.
“As he gathered clues, Scott-Railton put out calls for help to people he already knew, as well as strangers, creating a spontaneous army of online sleuths that numbers in the hundreds, if not the thousands,” says NPR.
As a result, they were able to identify the two men in body armor seen carrying plastic handcuffs, leading to their subsequent arrests.
A very large and diverse cadre of online sleuths is working around the lock to identify, blame and shame the insurrectionists. Some have been at it since Charlottesville and the Proud Boy riots.
Social media helped organize the assault on the U.S. Capitol building and social media is helping to bring down the mob.
As Phillip Bump says in the Washington Post, “The revolution wasn’t just televised, it was live-streamed.”
Fascinating report on Jan. 6 and its aftermath. I rejoice at the tech guys using the tch info so abundantly built into the Capitol building. Ignorance of the law is no excuse in the United States.
LikeLike